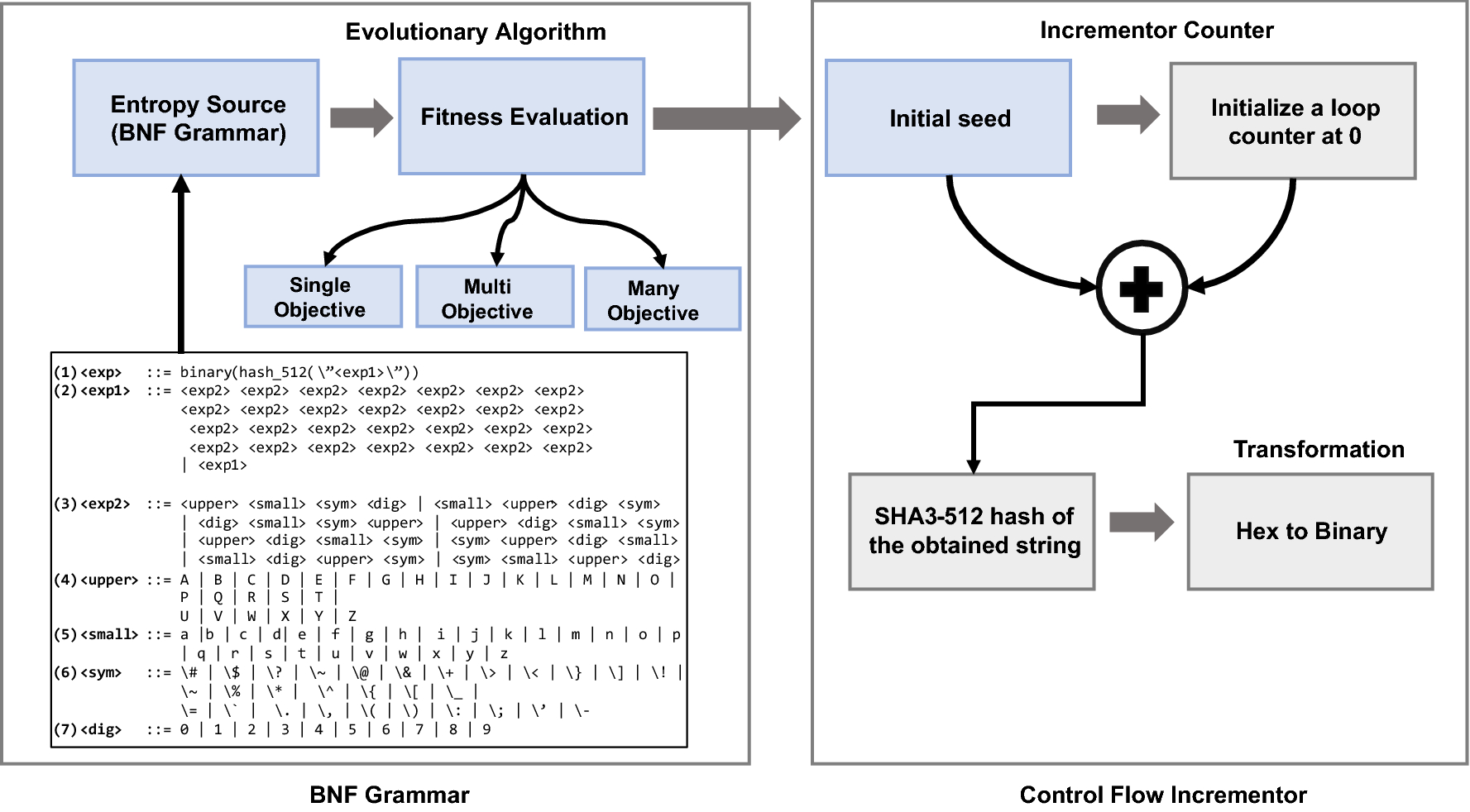
Design of a cryptographically secure pseudo random number generator with grammatical evolution | Scientific Reports
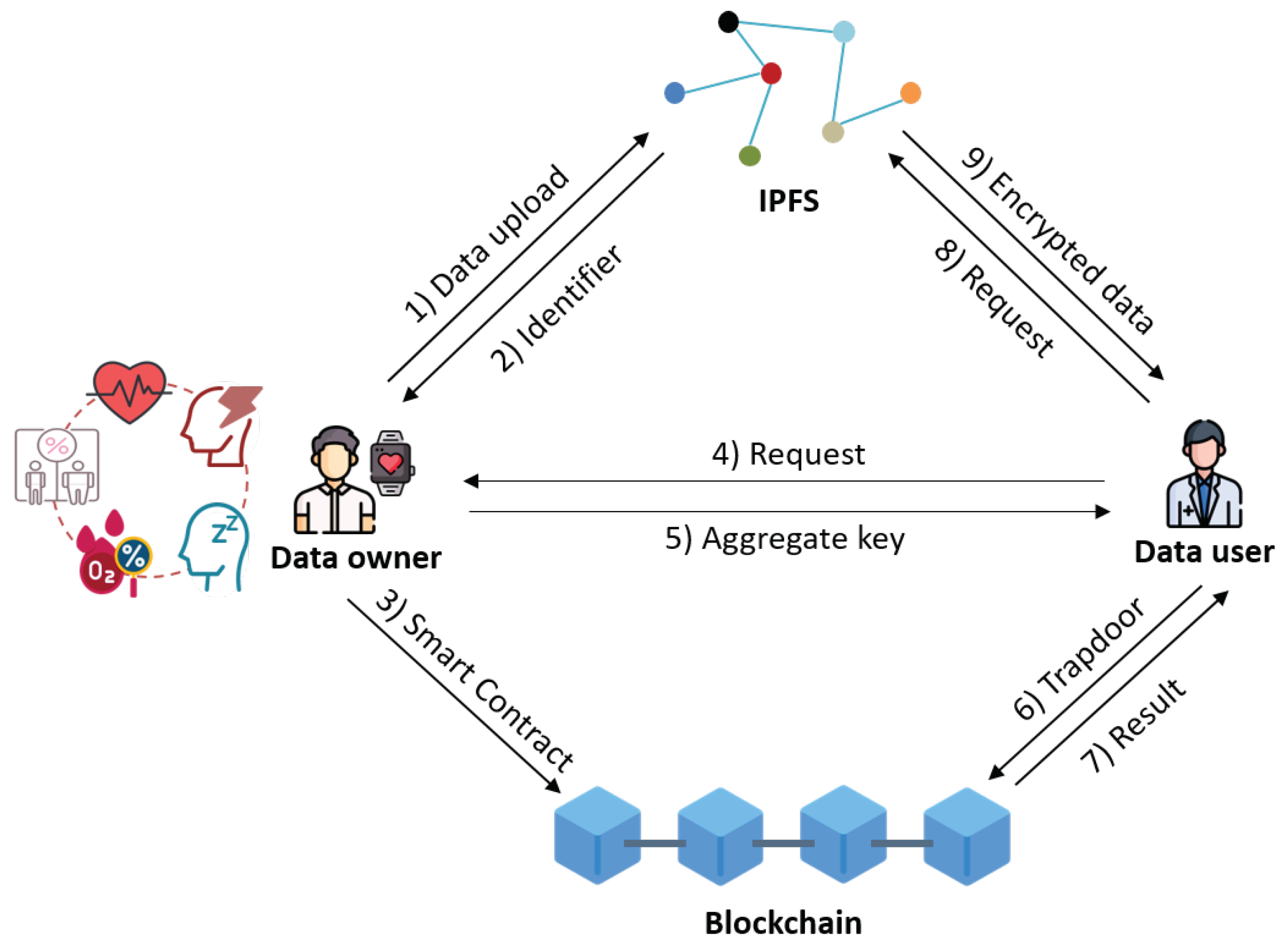
Electronics | Free Full-Text | A Secure Personal Health Record Sharing System with Key Aggregate Dynamic Searchable Encryption
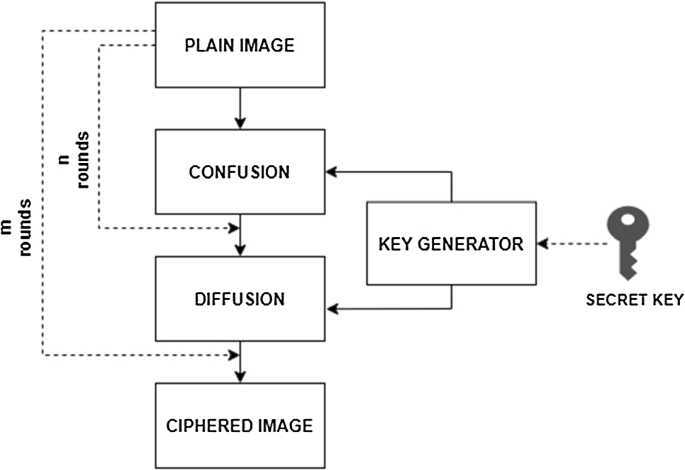
Survey on image encryption techniques using chaotic maps in spatial, transform and spatiotemporal domains | SpringerLink
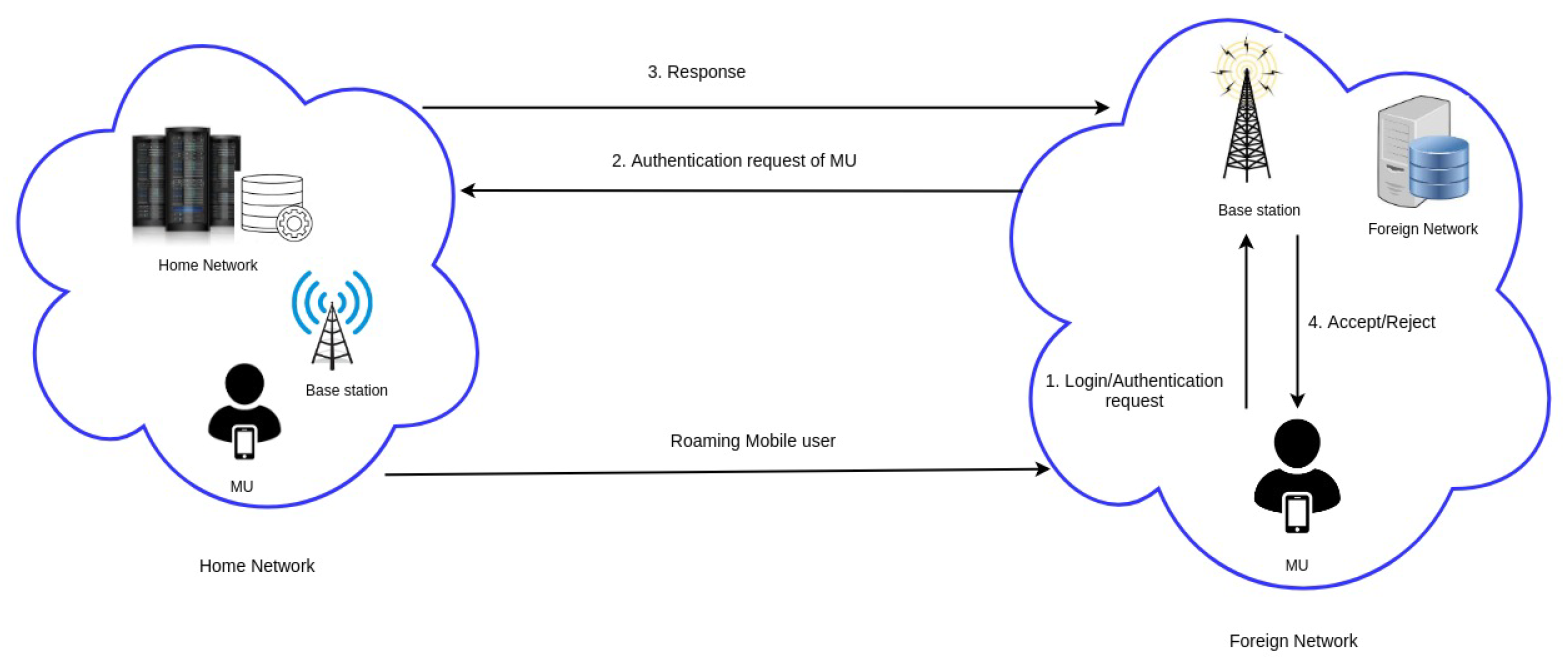
Cryptography | Free Full-Text | ES-HAS: ECC-Based Secure Handover Authentication Scheme for Roaming Mobile User in Global Mobility Networks
![An efficient multilevel security architecture for blockchain-based IoT networks using principles of cellular automata [PeerJ] An efficient multilevel security architecture for blockchain-based IoT networks using principles of cellular automata [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2022/cs-989/1/fig-2-full.png)
An efficient multilevel security architecture for blockchain-based IoT networks using principles of cellular automata [PeerJ]

Sustainability | Free Full-Text | Quantum Key Distribution Protocol Selector Based on Machine Learning for Next-Generation Networks
![PDF] A New Cryptographic Hash Function Based on Cellular Automata Rules 30 , 134 and Omega-Flip Network | Semantic Scholar PDF] A New Cryptographic Hash Function Based on Cellular Automata Rules 30 , 134 and Omega-Flip Network | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/1563c58daf7a9f63784ee19a98aeb529b7eb66bb/5-Table2-1.png)




![PDF] Cellular Automata and Cryptography | Semantic Scholar PDF] Cellular Automata and Cryptography | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/513f8c667fa015879356692c3e98f4fb8d052303/29-Figure2.5-1.png)





